1Why a Score Instead of a Finding List
Most domain security tools return findings. Lots of them. A typical audit of a mid-size organization's domain reveals missing DMARC enforcement, a weak SPF qualifier, unmonitored subdomains, expiring certificates, absent CAA records, and more — often 30 to 50 individual items at once. The analyst is then left with an unanswered question: where do I start?
A raw finding list has no inherent priority. Every item looks equally urgent — or equally ignorable. Critical gaps share the same visual weight as low-severity hardening notes. And if you have to report the situation to a CISO, a client, or a board, a list of technical identifiers is nearly impossible to communicate without extensive interpretation work.
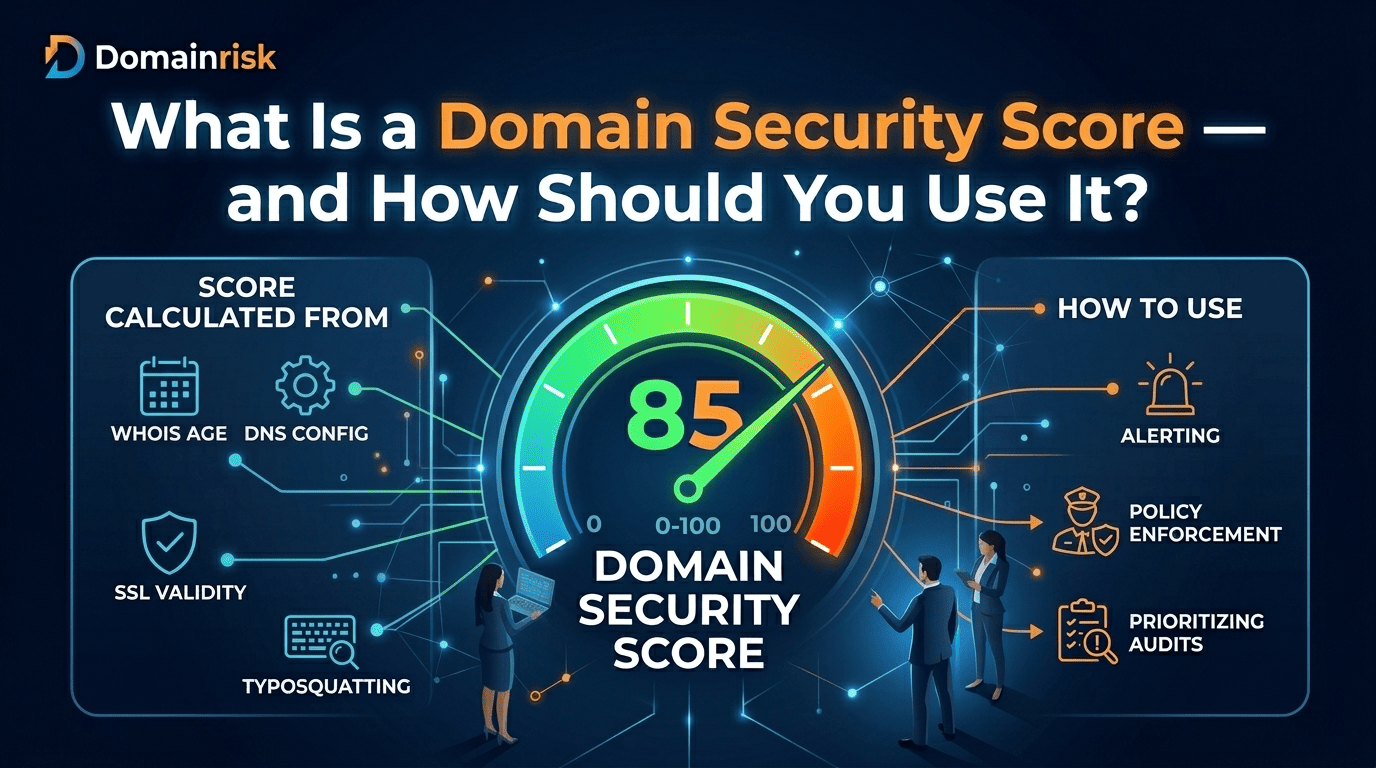
A score changes the conversation. It provides a single number that can be trended over time, compared across a portfolio of domains, benchmarked against an industry baseline, and understood immediately — even by someone who has never heard of MTA-STS or CAA records. The underlying findings remain accessible for the analysts who need them, but the score gives everyone else a clear entry point for decision-making.
Three things a score enables that a list cannot
- •Triage at a glance. Analysts instantly know which domain in a portfolio needs immediate attention without reading every finding.
- •Cross-domain comparison. A score makes it possible to rank 50 vendor domains or 200 monitored assets by risk level in seconds.
- •Executive communication. A score of 34/100 explains the urgency of a remediation budget request far more effectively than a spreadsheet of DNS misconfigurations.
2The Three Axes of Domain Risk
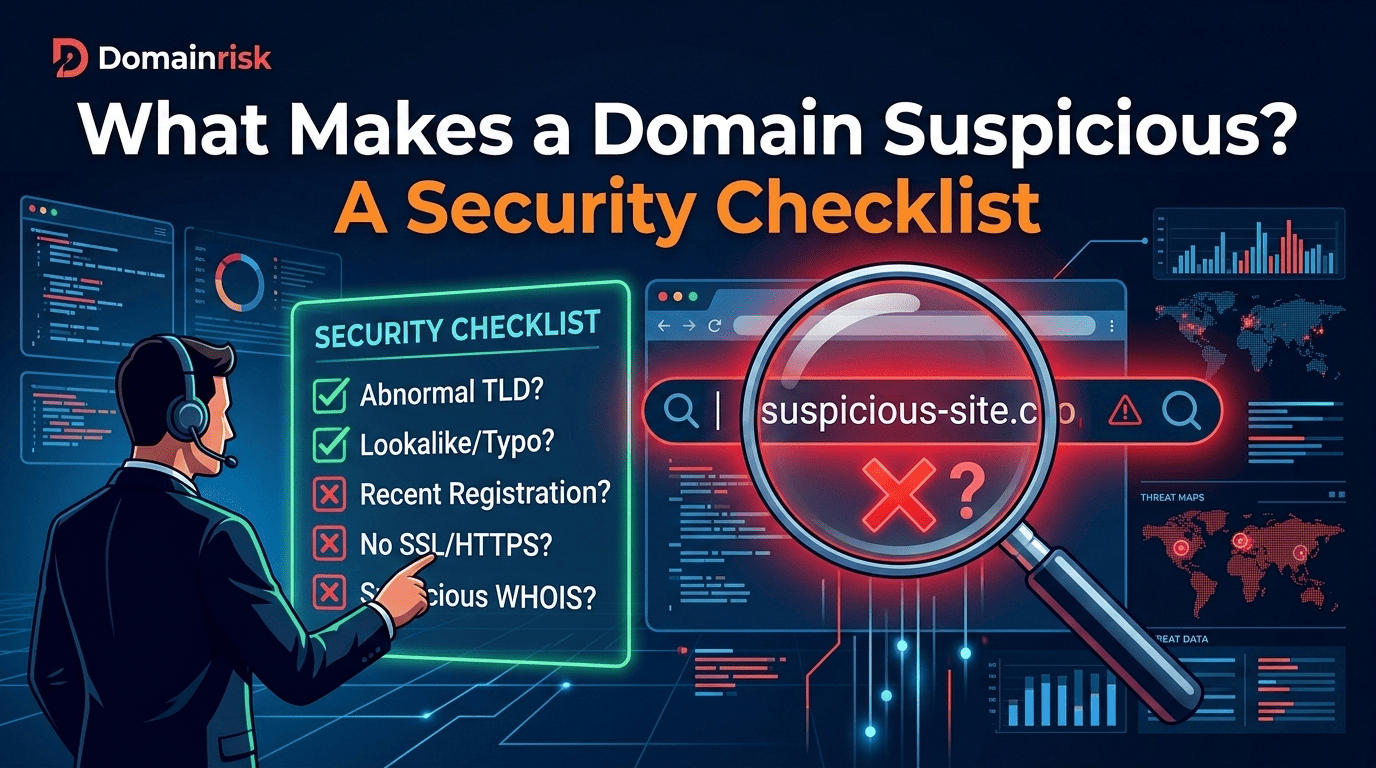
Not every security signal carries equal weight. A domain with no DMARC policy faces a different order of risk than a domain with a missing HSTS header. A valid score must reflect this difference — and it must do so transparently, so analysts can understand why a score is what it is and where to focus remediation effort.
DomainRisk.io structures its scoring around three axes, each representing a distinct dimension of domain risk. The weighting is intentional and reflects real-world threat data on what attackers actually exploit versus what represents best-practice hardening.
The heaviest axis — because these are the findings attackers can exploit directly, today. This includes missing or misconfigured DMARC and SPF policies that enable email spoofing, unmonitored subdomains vulnerable to takeover, exposed sensitive DNS records, and other conditions that represent an active attack surface rather than a theoretical gap.
Exploitable risk findings are weighted at 50% because they represent the difference between a domain that is merely imperfect and one that is actively weaponizable. A domain can score well on the other two axes and still be critically exposed if this axis is weak.
Security controls that are present but not fully enforced, or missing but not yet exploitable. This axis captures CAA records that restrict certificate issuance, HSTS headers with insufficient max-age, DMARC policies still at p=none, and MTA-STS configurations that exist but have not been set to enforce mode.
These findings will not cause an immediate breach — but they leave the domain without defence-in-depth. They are the gaps that become critical when something else fails. Weighted at 30% to reflect their real but secondary urgency.
Registration hygiene, WHOIS accuracy, registrar lock status, renewal posture, and documentation completeness. Governance findings rarely represent an immediate exploit path — but they signal organizational maturity and the likelihood that security controls are being maintained systematically rather than reactively.
Weighted at 20% because governance gaps are lagging indicators of future risk rather than present exposure. They matter significantly in vendor due diligence and compliance contexts where posture, not just current state, is evaluated.
3What the Numbers Actually Mean
Score thresholds are only useful if they map to actionable states. The four bands below reflect distinct risk postures — not arbitrary quartiles — and each corresponds to a different operational response.
Healthy Posture
Core controls are in place and enforced. Routine maintenance applies — monitor certificate expiry, check for drift after infrastructure changes, verify DMARC reports. No immediate action required.
Gaps Identified
Meaningful security gaps are present. Remediation is recommended on a defined schedule. At this level, the domain is not fully hardened and may be exposed to specific attack vectors depending on which findings are open.
Significant Exposure
Multiple unresolved findings across high-weighted axes. The domain represents a real attack surface. Remediation should be prioritised and tracked. This band often flags domains with no DMARC enforcement, dangling DNS records, or expired certificate controls.
Critical — Active Flaw
One or more critical exploitable findings are active. Immediate response is required. At this level, the domain may already be in use as a spoofing vector or attack staging point. Do not treat this as a remediation backlog — treat it as an incident.
A score in the 50–79 range does not mean a domain is safe — it means it is imperfect in ways that are not yet critical. The gap between 79 and 80 is not meaningful. What matters is the direction of travel and which specific findings are holding the score down.
4The Critical Guardrail
A composite score introduces a specific failure mode: it can average away a catastrophic vulnerability. Imagine a domain that is otherwise well-configured — enforced DMARC, locked registrar, HSTS in place, clean subdomains. Then suppose a single critical finding exists: an active subdomain CNAME pointing to a decommissioned cloud service, ready to be claimed by an attacker in under an hour. The overall score might still land at 78/100. That number looks manageable. It is not.
The guardrail rule
Any finding classified as critical — regardless of its impact on the composite score — triggers a separate severity indicator that overrides the score interpretation. A domain with a critical open finding is always treated as critical, even if its score reads 90/100.
DomainRisk.io surfaces this guardrail explicitly. The score is never the only signal — critical findings are always called out distinctly, so a high composite number cannot hide a single exploitable flaw. The score tells you the overall posture; the guardrail tells you whether that posture is currently irrelevant.
This distinction matters most in automated workflows — SOC alert rules, vendor risk thresholds, MSSP SLA triggers. If your process only reads the composite score, you will miss the cases where a single finding overrules everything else. Always configure critical-finding alerts independently of score thresholds.
5Score Drift and Volatility
A score taken at a single point in time has limited value. A domain that scored 85 last month and scores 71 today is telling you something important — and it is not just that seven findings appeared. It is that something changed. Infrastructure was modified, a certificate was replaced, a new mail-sending service was added, a subdomain was spun up and never secured. The score moved because the domain's posture changed.
Score drift — the delta between two consecutive measurements — is often more informative than the absolute score. A stable 65 over 90 days indicates a known, static risk that is being tolerated. A score that swings from 82 to 55 overnight indicates instability: something happened, and you probably do not know what.
What high volatility reveals
- •Frequent infrastructure changes without a corresponding security review process
- •Certificate or DNS record churn that opens temporary gaps in coverage
- •Uncontrolled third-party access to DNS or hosting, creating unpredictable configurations
- •Absence of a change management process for domain-related assets
DomainRisk.io tracks score history and computes a Volatility Score alongside the security score — a measure of how much a domain's posture has fluctuated over the monitoring window. A domain with a high Volatility Score is an unstable domain, regardless of where the composite score sits today. Instability is itself a risk signal.
6How to Use Your Score in Practice
A score is only as useful as the workflow it feeds. Here are three concrete scenarios where the domain security score changes the way teams operate.
When an alert fires on a suspicious domain — in an email header, a phishing report, a network log — the first question is always: how risky is this domain? Running a full manual assessment takes time the SOC does not have during an active incident.
A domain security score gives Tier-1 analysts an immediate risk context in seconds. A domain scoring below 30 with an active critical finding is treated as confirmed-hostile infrastructure until proven otherwise. A domain scoring above 80 with no critical flags is deprioritised. The score does not replace analysis — it routes it, so analysts spend time on the cases that warrant it.
Third-party risk assessments traditionally rely on questionnaires — self-reported, slow, and easily gamed. A domain security score introduces objective, independently verifiable evidence into the process.
Before onboarding a vendor or renewing a contract, run their primary domain through DomainRisk.io. A vendor with no DMARC enforcement, unlocked registrar, and a history of score volatility is demonstrating through observable technical evidence that their security posture is either weak or unstable — regardless of what their security questionnaire says. Score thresholds can be formalised into procurement policies: vendors below 50 must remediate before contract signature.
Security service providers managing domain portfolios for multiple clients face a communication problem: how do you convey a complex, multi-vector risk posture to clients who are not security specialists?
A domain security score translates directly into client-facing reporting. Month-over-month score trends show remediation progress. Score comparisons across a client's domain portfolio identify which assets are under-invested. The guardrail mechanism ensures that a critical vulnerability is never buried under a reassuring composite number. Clients can understand a score of 48/100 without needing to read a technical finding report — and that understanding drives faster remediation approvals.
Conclusion
A domain security score is not a replacement for detailed findings — it is a navigation layer on top of them. It tells you where to look first, how severe the situation is, whether posture is improving or degrading over time, and when a single critical flaw overrides everything else.
The value of the score lives in three things: transparent weighting across exploitable risk, hardening gaps, and governance; a guardrail mechanism that prevents critical findings from hiding behind a comfortable average; and continuous monitoring that turns a snapshot into a trend.
Used correctly, a domain security score is the difference between a security team that reacts to incidents and one that sees degradation before attackers do.
Run your first scan and get your domain security score in under 60 seconds.
DomainRisk.io evaluates your domain across all three axes — exploitable risk, hardening gaps, and governance — and surfaces both the composite score and any critical guardrail findings instantly.