1Registration Age
A domain registered fewer than 30 days ago is statistically the single strongest individual predictor of malicious intent. Threat intelligence datasets consistently show that the vast majority of phishing domains and BEC infrastructure are used within days of registration — before reputation systems, blocklists, and email filters have had time to catch up. Attackers exploit this window deliberately.
To check: a standard WHOIS lookup on the domain name returns aCreation Datefield. For domains where the registrar enforces GDPR redaction on all fields, certificate transparency logs (crt.sh) often expose the first certificate issuance date, which serves as a reliable lower bound. APIs likewhoisjson.comreturn parsed WHOIS data including registration dates in a machine-readable format, making age checks trivial to automate at scale.
What a fresh domain reveals
A brand-new domain has zero reputation history. It has never been seen in email flows, web crawls, or threat feeds. Security products that rely on historical data — reputation scores, category classifiers, age-based trust — treat it as an unknown, which is often equivalent to trusted. Attackers know this. A 5-day-old domain carrying a convincing brand name and a valid SSL certificate will bypass most perimeter defenses.
Critical
Active campaign window. The domain was almost certainly registered specifically for this attack.
High
Still well within the high-risk window. Most legitimate domains do not go live within a month of registration.
Medium
Elevated caution warranted, especially when combined with other risk signals.
Low (baseline)
Age alone is no longer a strong signal. Other indicators take precedence.
2Registrar Reputation
Not all domain registrars are equal from a security standpoint. Threat intelligence research consistently identifies a small subset of registrars that are disproportionately represented in phishing kits, spam campaigns, and malware infrastructure. This is not coincidence — it reflects deliberate choices by operators of malicious infrastructure: low prices, minimal identity verification, permissive abuse response policies, and privacy protection included by default.
The WHOISRegistrarfield identifies who sold the domain. Cross-referencing that name against published abuse rate datasets — from sources like Spamhaus, APWG, or academic phishing studies — tells you whether you are dealing with infrastructure registered through a high-risk channel.
Signals to watch
- •Registrar appears frequently in active phishing or spam blocklists (Spamhaus DBL, SURBL, URIBL)
- •Registrar has a documented history of slow or non-existent abuse complaint response
- •Free or near-free registration tiers with no identity verification requirement
- •Bulk registration APIs with no rate limiting or fraud detection
Context matters
A domain registered through a high-abuse-rate registrar is not automatically malicious — many legitimate domains use the same services. What matters is the combination: a fresh domain, registered through a known-abused registrar, with WHOIS privacy enabled, pointing at disposable mail infrastructure. Each signal adds weight to the composite picture.
3WHOIS Privacy & Redaction
Since GDPR implementation in 2018, the majority of newly registered domains show heavily redacted WHOIS records. Registrant name, email, address, and phone number are routinely replaced with privacy service proxies or generic placeholders. This isentirely legitimate in most cases— privacy protection is a reasonable default for any individual or small business registering a domain. Treating all private registrations as suspicious would produce an unacceptably high false-positive rate.
The question is not whether WHOIS is private, butwhat other signals accompany that privacy.A 4-year-old domain with WHOIS privacy and a complete, consistent DNS configuration is almost certainly legitimate. A 3-day-old domain with WHOIS privacy, no SPF record, and an MX pointing at a disposable mail provider is a very different matter.
Typical legitimate profile
• Domain age: 2+ years• WHOIS privacy: enabled (GDPR standard)• Registrar: major, low-abuse-rate provider• SPF, DMARC: present and enforced• SSL: issued to a recognizable organization• Consistent nameservers over time
Suspicious profile
• Domain age: <15 days• WHOIS privacy: enabled• Registrar: documented in phishing datasets• SPF: missing. DMARC: missing• SSL: Let's Encrypt, issued same day as registration• MX: points to a temporary mail service
The redaction gap: what you can still learn
Even with full WHOIS redaction, several fields remain useful. TheCreation Date,Updated Date,Expiry Date, registrar name, and nameservers are typically preserved. An expiry date set exactly 1 year out on a brand-new domain (the default minimum) is consistent with a throwaway campaign domain. An expiry date set 5 years out suggests a legitimate long-term investment — or a well-resourced threat actor.
4DNS Configuration
The DNS records of a domain reveal a great deal about the intent behind it. Legitimate organizations building email infrastructure invest time in configuring SPF, DKIM, and DMARC — not because they want to, but because they need deliverability. Attackers registering throwaway phishing domains have no such incentive. The resulting DNS profile is predictably sparse.
Missing or absent SPF & DMARC
A domain with no SPF record can be spoofed by anyone — any mail server in the world can send email that appears to originate from that domain. A domain with no DMARC record applies no policy to failed authentication, meaning even when SPF fails, mail still gets delivered. Together, their absence is one of the most reliable markers of a domain set up for abuse rather than legitimate communication.
MX records pointing to disposable services
When a suspicious domain's MX record points to providers like Mailinator, Guerrilla Mail, Temp Mail, or similar disposable inbox services, the intent is clear: the domain is designed to receive but not be held accountable for. These providers delete inboxes automatically and maintain no identity records.
$ dig MX secure-paypal-verify.com
secure-paypal-verify.com. 300 IN MX 10 mailinator.com.
Abnormally low TTL values
A DNS TTL of 60–300 seconds on an A record is a strong operational signal: the operator expects to change the IP address frequently and needs changes to propagate within minutes. For legitimate CDN or load-balancing use cases, this is normal. For a freshly registered domain with no other infrastructure, it suggests fast-flux DNS — a technique used to rotate C2 server IPs rapidly to evade blocklists and takedown requests.
# SPF record: missing
No TXT record found containing "v=spf1"
# DMARC record: missing
No TXT record found at _dmarc.secure-paypal-verify.com
# A record TTL: 60 seconds (fast-flux indicator)
secure-paypal-verify.com. 60 IN A 185.234.xx.xx
# Risk: HIGH — absent email auth + ultra-low TTL + 4 days old
5SSL Certificate
The padlock icon in a browser address bar has become the single most misunderstood security indicator in existence. HTTPS confirms that theconnection is encrypted— it says nothing whatsoever about the trustworthiness of thedestination.Let's Encrypt issues free, automated certificates to any domain that can demonstrate DNS control. A phishing site resolving tohttps://secure-login.paypa1.comwill have a perfectly valid certificate and a green padlock.
What SSL does tell you
• The connection is encrypted in transit• The issuing CA has verified domain control• Certificate issuance date (lower bound for domain activity)• Subject Alternative Names (other domains on same cert)• Organization name for EV certificates (rare but meaningful)
What SSL does NOT tell you
• Whether the destination is legitimate or malicious• Whether the domain operator has any identity verification• Whether the content is safe• Whether the domain is who it claims to be• Anything about the reputation of the registrant
What to analyze in a certificate
- Certificate age: a cert issued within days of domain registration confirms the domain went live immediately — consistent with a prepared phishing kit deployment
- Issuer: Let's Encrypt or ZeroSSL with no OV or EV validation means zero identity verification. Any entity that controls the domain can get this cert.
- Subject Alternative Names (SANs): a single cert covering dozens of domains often indicates a shared phishing hosting provider or a bulletproof hosting service running campaigns at scale
- Certificate Transparency logs: crt.sh indexes every publicly issued certificate. A domain that has been reissuing certs every few days has been cycling infrastructure — a classic evasion pattern
The attacker's certificate strategy
Sophisticated campaigns now issue certificates for hundreds of lookalike domains in a single batch. Certificate transparency logs expose this pattern in real time — which is exactly why monitoring CT logs for your brand names is an effective early-warning mechanism for impersonation campaigns in preparation.
6Typosquatting & Brand Impersonation
The domain name itself is the most immediately readable signal. Impersonation attacks rely on a simple cognitive exploit: users glancing at a URL in a phishing email or a browser address bar will noticepaypal.comand misspaypa1.com. The techniques used to construct these domains are well-documented and algorithmically detectable.
Levenshtein distance mutations
Character substitutions, transpositions, insertions, and deletions that produce a domain visually close to the target. A Levenshtein distance of 1 or 2 from a known brand name is a strong impersonation signal.
Homoglyph substitution
Replacing Latin characters with visually identical Unicode characters from other scripts (Cyrillic, Greek, etc.). Modern browsers show the Punycode representation in the address bar, but many users — and some email clients — do not.
Keyword augmentation
Appending or prepending trust-signaling keywords to the brand name. The goal is to make the domain read as an official subdomain or security page of the target brand.
TLD abuse
Registering the same brand name under a different or uncommon TLD. Users trained to recognize.com often overlook suspicious TLD choices on otherwise identical domain names.
Automating impersonation detection
Manual review does not scale. The volume of lookalike domains registered daily far exceeds any analyst capacity. Automated detection requires computing fuzzy string distances against a dictionary of protected brand names, normalizing Unicode before comparison, and monitoring certificate transparency logs for new domains that match impersonation patterns. This is the core of what domain monitoring platforms like DomainRisk.io do continuously.
7Subdomain Activity
Once an attacker controls a convincing lookalike apex domain, they rarely stop at a single hostname. A sophisticated phishing or BEC campaign will generate dozens of subdomains under the same apex — each one targeting a different brand, department, or victim profile. The subdomain structure of a suspicious domain is therefore highly revealing.
Rapid creation velocity
Dozens of subdomains appearing within hours of domain registration. Legitimate organizations ramp subdomain usage gradually. A burst of subdomains on day 1 is a campaign deployment signature.
Trust-signaling names
Subdomains named login., secure., account., verify., support., portal., auth., update. are designed to look like authenticated entry points for the impersonated brand.
Target-specific naming
login.paypal-secure[.]com, account.netflix-update[.]net, verify.apple-id-support[.]org — the subdomain encodes the specific brand being impersonated, while the apex domain provides the overall deceptive frame.
Random or algorithmically generated subdomains
Long strings of random characters as subdomains (e.g. a3f7c2d1.malicious-domain.com) often indicate a Domain Generation Algorithm (DGA) used for C2 communications, not phishing.
Certificate transparency as a subdomain telescope
Every certificate issued for a subdomain is logged in public CT logs. Querying crt.sh for a suspicious apex domain reveals the full subdomain portfolio — including subdomains that may not be publicly linked or easily discoverable through DNS enumeration alone. For a newly registered suspicious domain, a CT log search that returns 40 subdomains is a definitive campaign indicator.
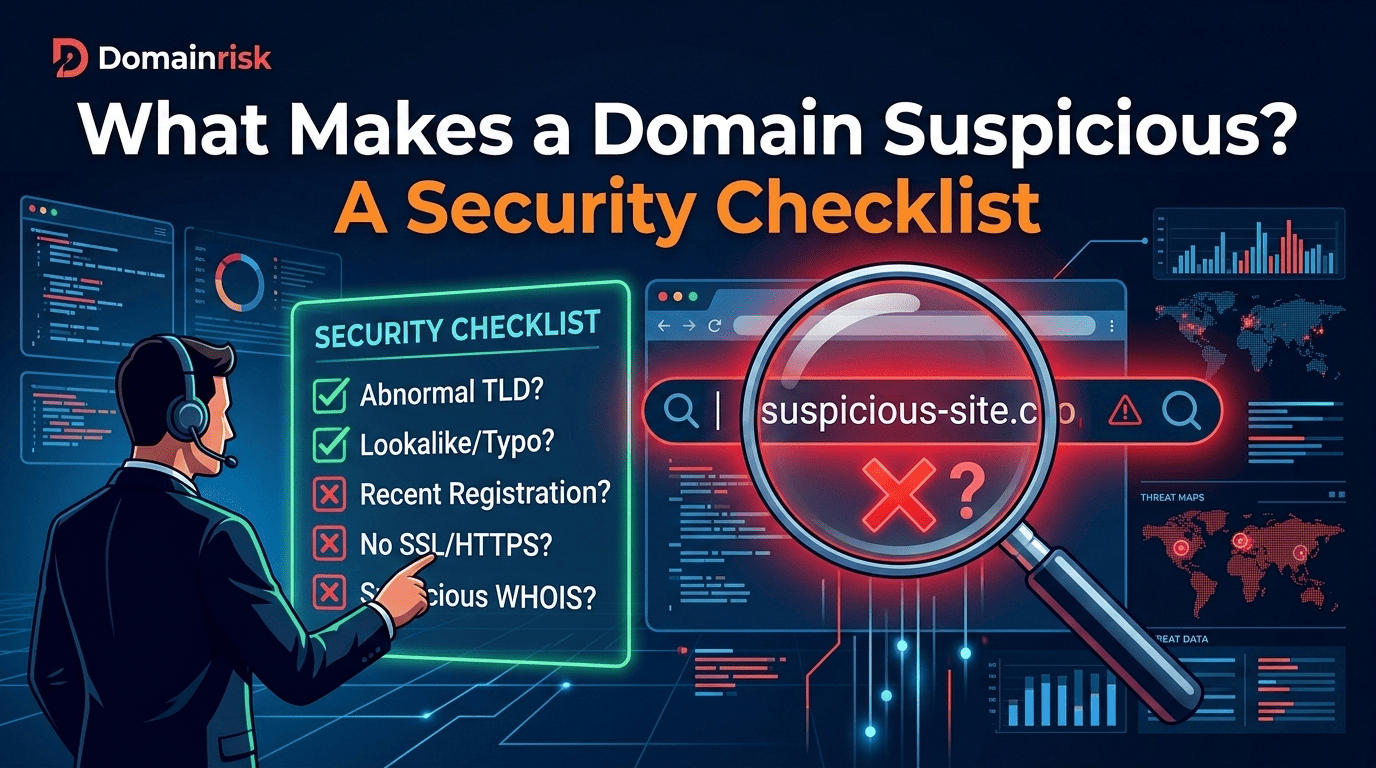
The Composite Risk Score
None of the seven signals above is sufficient on its own. A 3-day-old domain could be a legitimate product launch. A Let's Encrypt certificate is the correct choice for thousands of legitimate small sites. WHOIS privacy is the standard for most registrations since 2018. Treating any individual signal as a binary verdict produces both excessive false positives and dangerous false negatives.
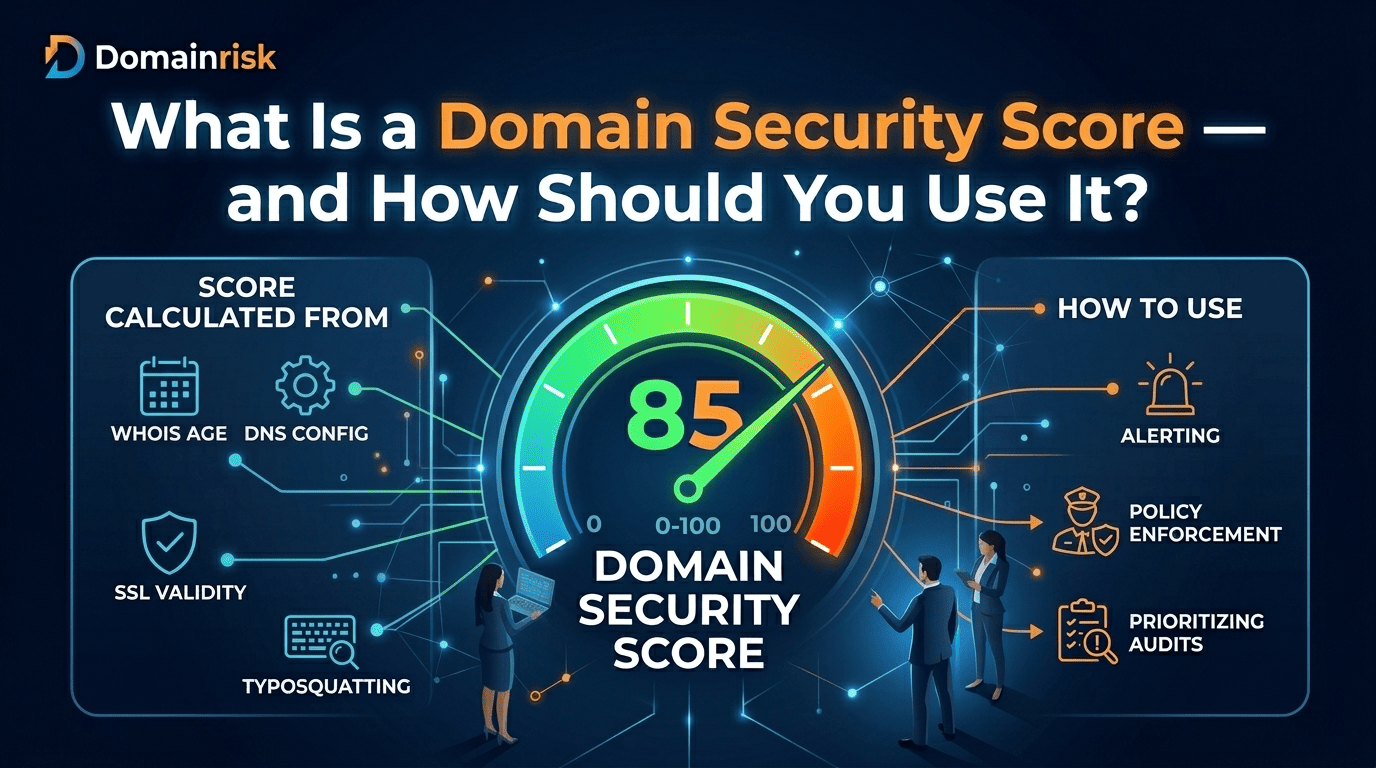
What matters is theweighted combinationof signals — and the degree to which they mutually reinforce each other. A domain that scores poorly on three or more independent dimensions is statistically very unlikely to be legitimate. Risk scoring models used by threat intelligence platforms assign weights to each signal and produce a composite score that reflects the overall suspicion level.
Running this checklist manually does not scale
DomainRisk.io aggregates all seven signals automatically — WHOIS age, registrar reputation, DNS email authentication, SSL certificate metadata, typosquatting distance against your protected brands, and subdomain proliferation — into a single risk score updated continuously. No spreadsheets. No manual WHOIS queries. No missed signals.
✓Conclusion
Domain suspicion is a multi-dimensional verdict.
No single indicator — not even a 2-day-old domain with a name that is one character away from a major bank — is proof of malicious intent. But when registration age, registrar reputation, WHOIS opacity, absent email authentication, a suspicious SSL profile, a brand-adjacent name, and rapid subdomain creation all point in the same direction, the probability of legitimate intent collapses to near zero.
The security value of this checklist lies in its systematic application. Human analysts reviewing individual domains in isolation will miss patterns. Automated systems that score domains against all seven dimensions simultaneously — and alert on composite thresholds rather than individual signals — catch campaigns that would otherwise slip through until the first victim clicks.
Two tools to help you operationalize this at scale:
DomainRisk.io
Full automated domain risk assessment — WHOIS, DNS, SSL, typosquatting detection, subdomain monitoring, and continuous alerting. For security teams that need an answer in under 60 seconds without writing a single query.
whoisjson.com
Structured WHOIS API with parsed creation dates, registrar data, and expiry fields in JSON. For teams building their own domain risk pipeline or enriching SIEM/SOAR alerts with registration context automatically.